Understanding G Network Configuration for Network Segmentation and Isolation
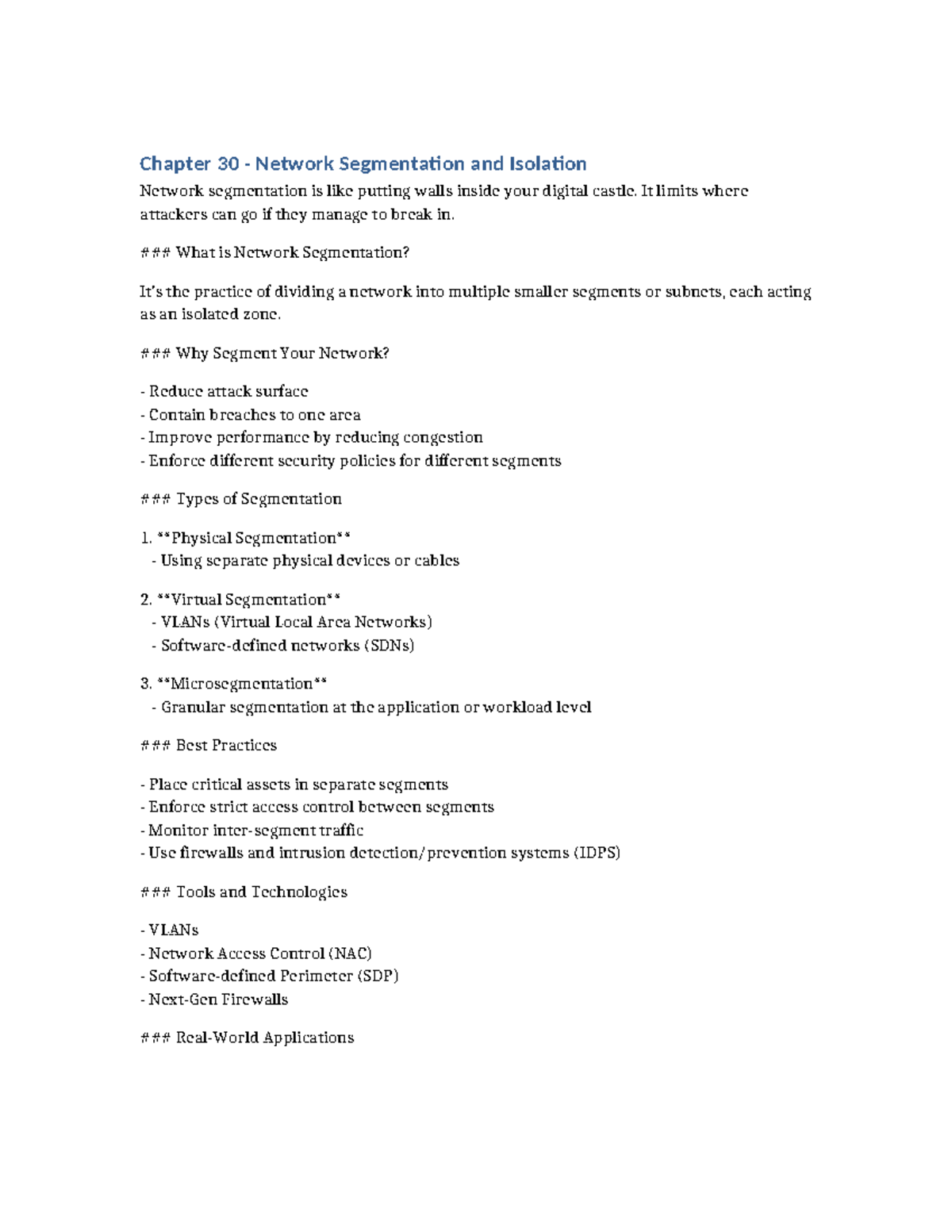
In today's complex networked world, ensuring the security and efficiency of your network is crucial. Network segmentation and isolation are two critical concepts that help achieve this goal. In this article, we'll explore the importance of G Network Configuration for Network Segmentation and Isolation, and discuss how it can be implemented.What is G Network Configuration for Network Segmentation and Isolation?
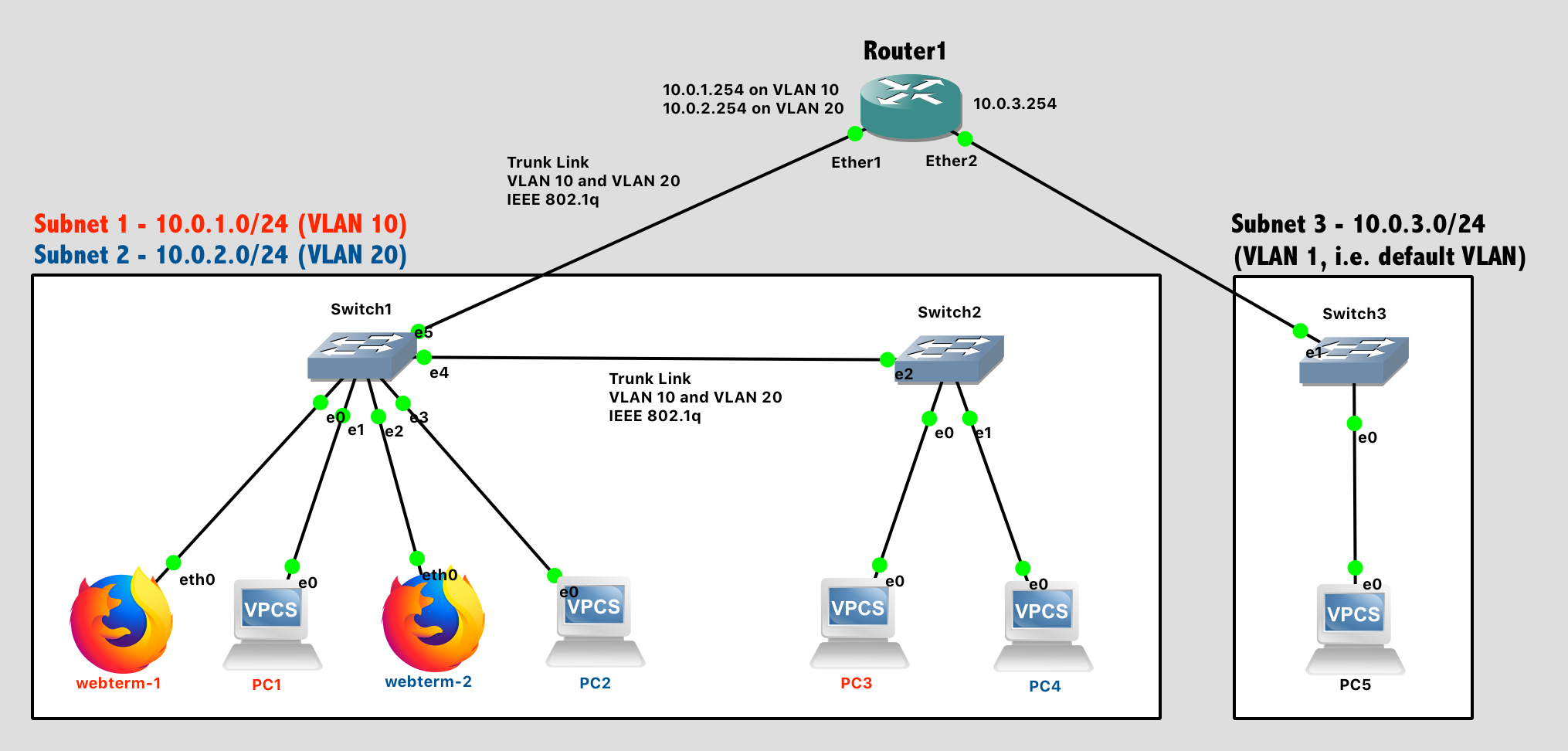
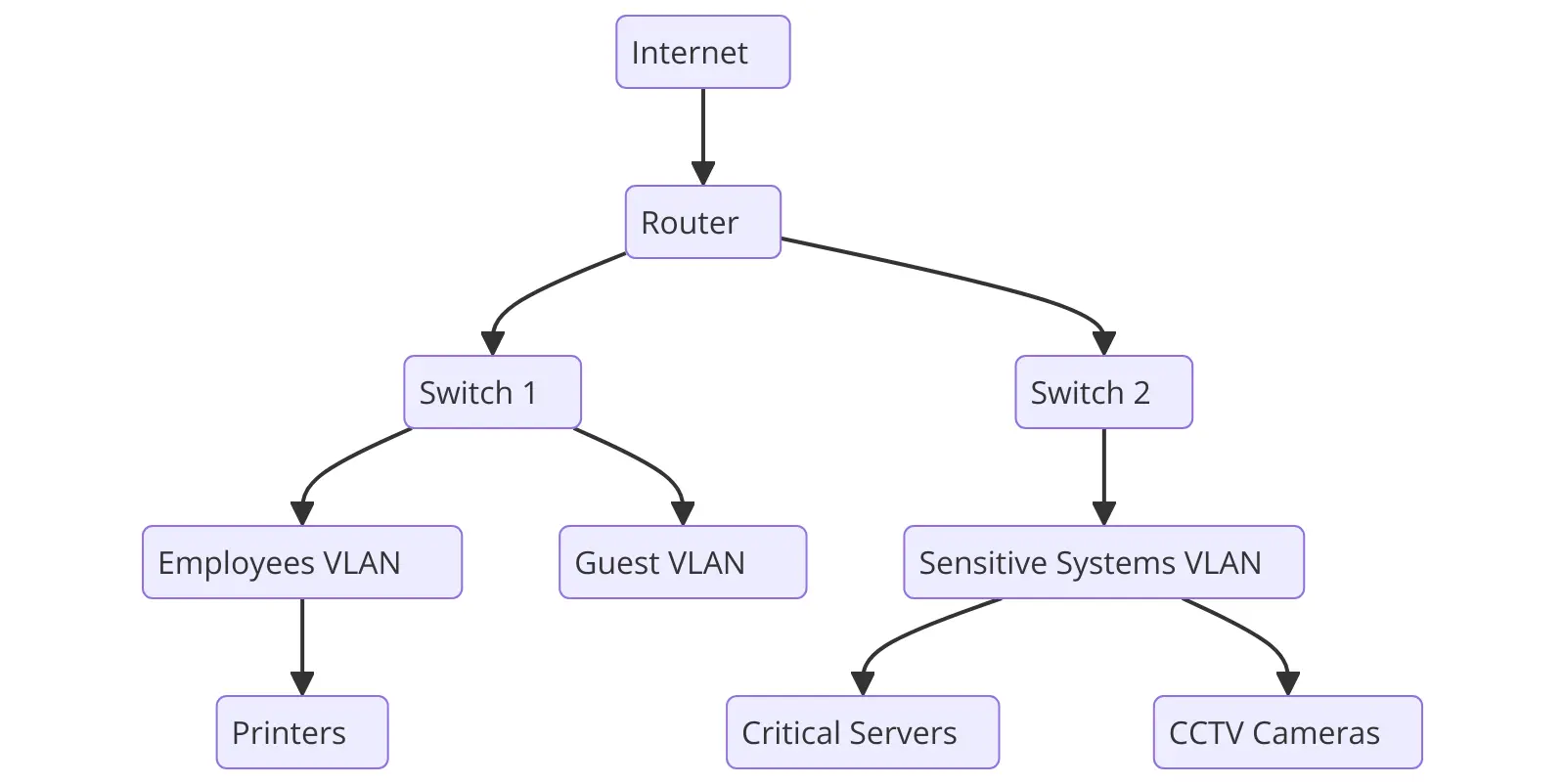
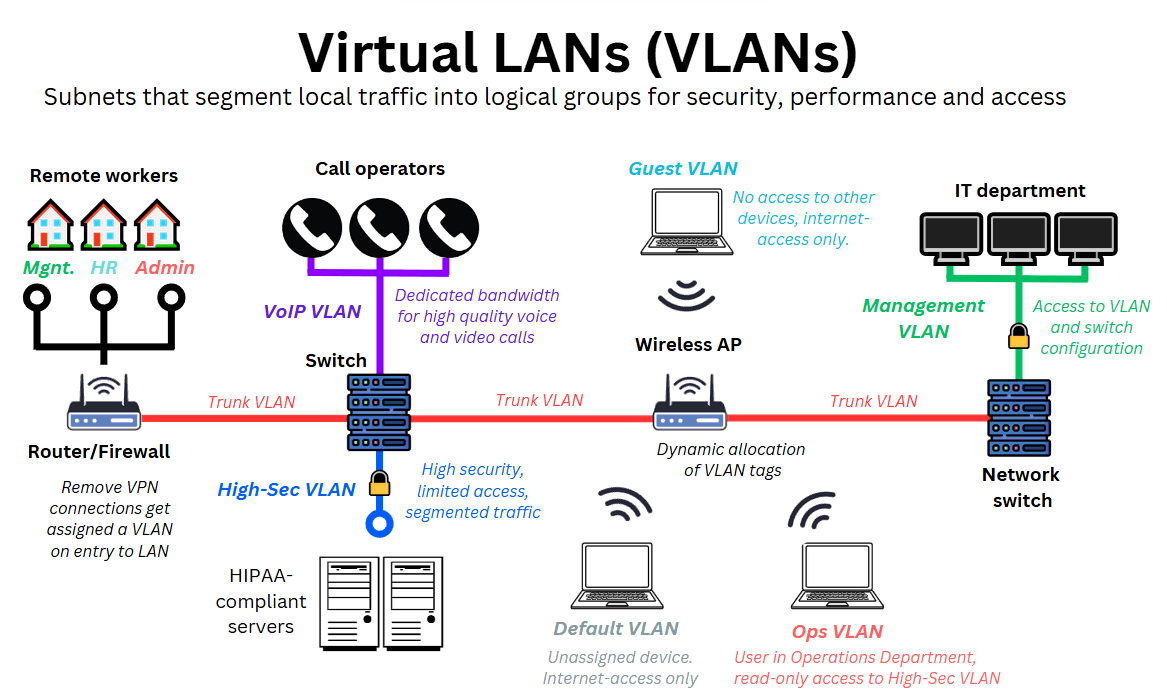
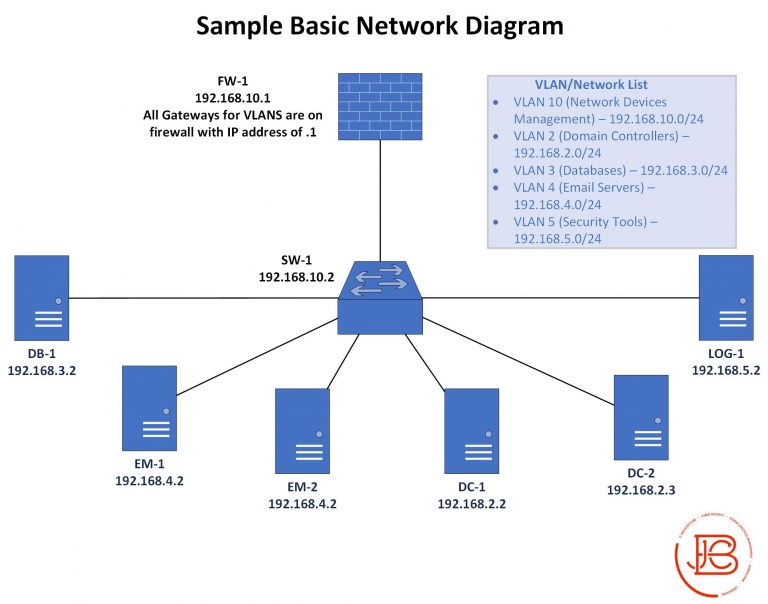
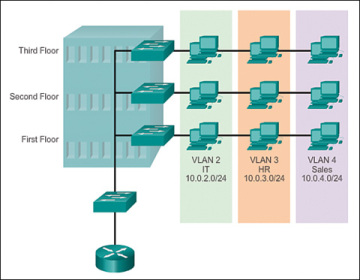
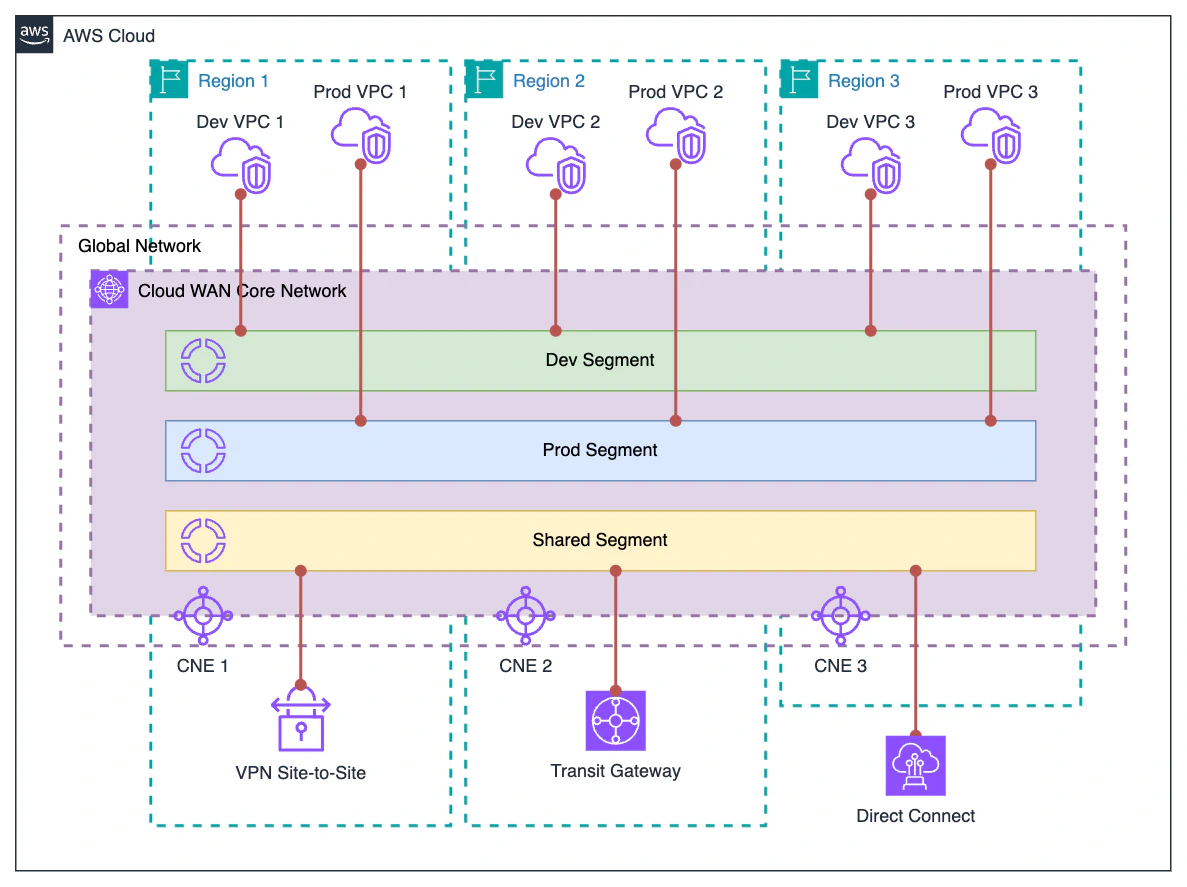
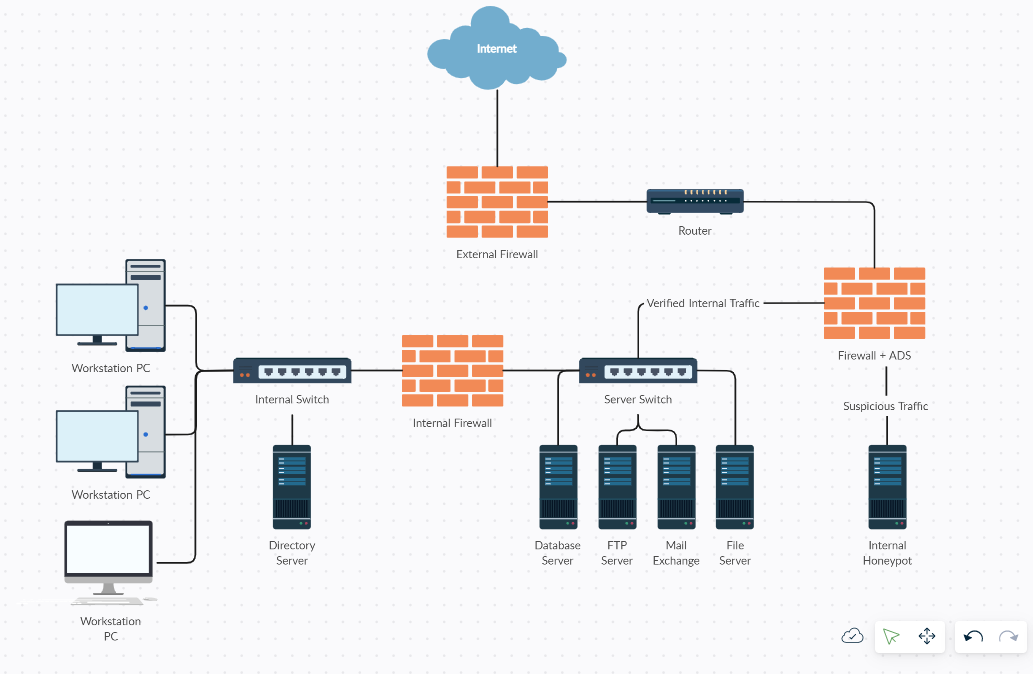
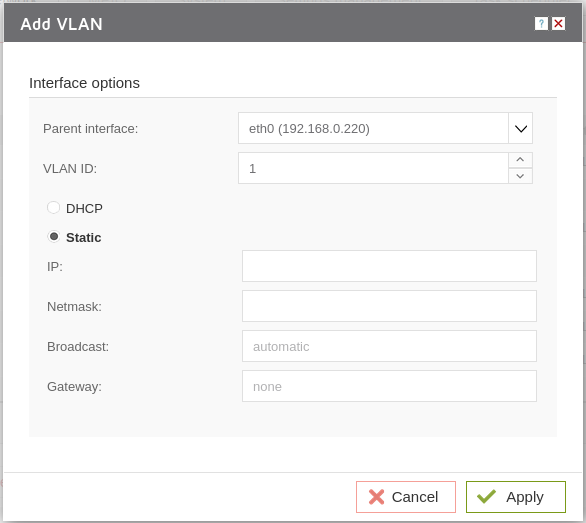
G Network Configuration for Network Segmentation and Isolation involves designing and setting up a network architecture that allows for the division of a single network into smaller, isolated segments. This is achieved through the use of virtual local area networks (VLANs), subnets, firewalls, and zones. The main goal is to create a secure and efficient network by limiting access, containing potential threats, and enhancing performance.Benefits of G Network Configuration for Network Segmentation and Isolation
Implementing G Network Configuration for Network Segmentation and Isolation offers numerous benefits, including: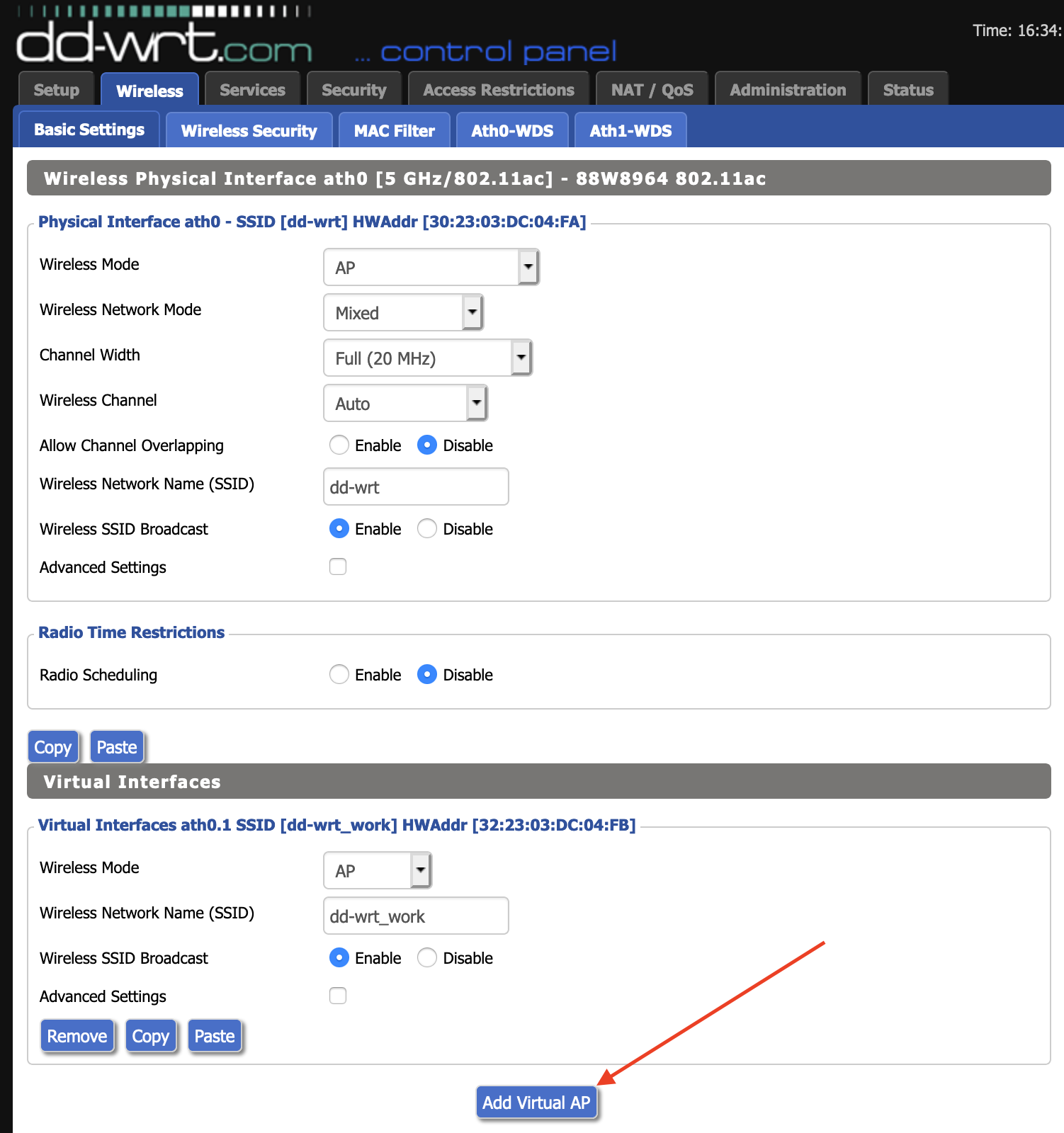
Best Practices for G Network Configuration for Network Segmentation and Isolation
To effectively implement G Network Configuration for Network Segmentation and Isolation, follow these best practices:1. Determine the Segmentation Strategy
Decide on the segmentation strategy that best suits your organization's needs, such as VLANs, subnets, firewalls, or zones.2. Perform Audits and Reviews
Conduct regular audits and reviews to assess current configurations, identify gaps, and ensure consistency.3. Produce a Company-Wide Access Control Policy
Such details provide a deeper understanding and appreciation for G Network Configuration For Network Segmentation And Isolation.
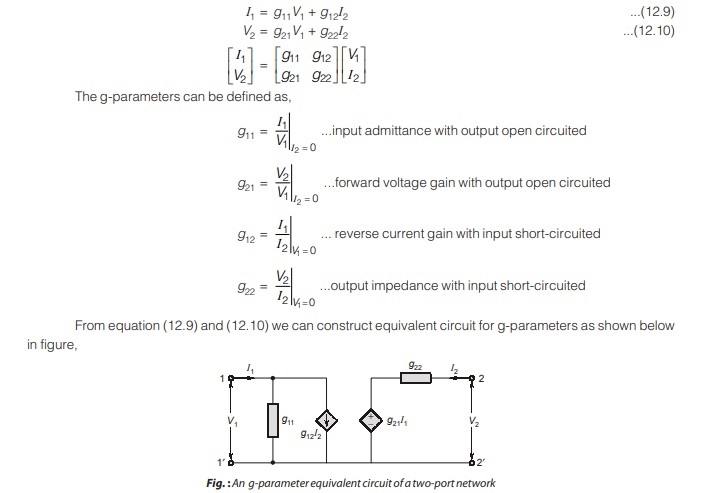
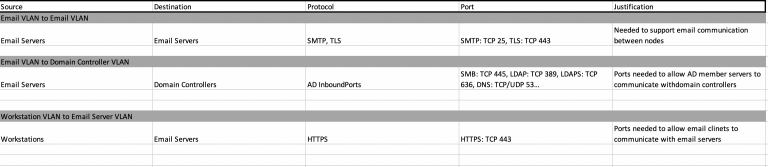
Define who can access what, ensuring least privilege and strict access controls. Divide your network into separate zones, each with its own set of access controls and security rules.Key Techniques for G Network Configuration for Network Segmentation and Isolation
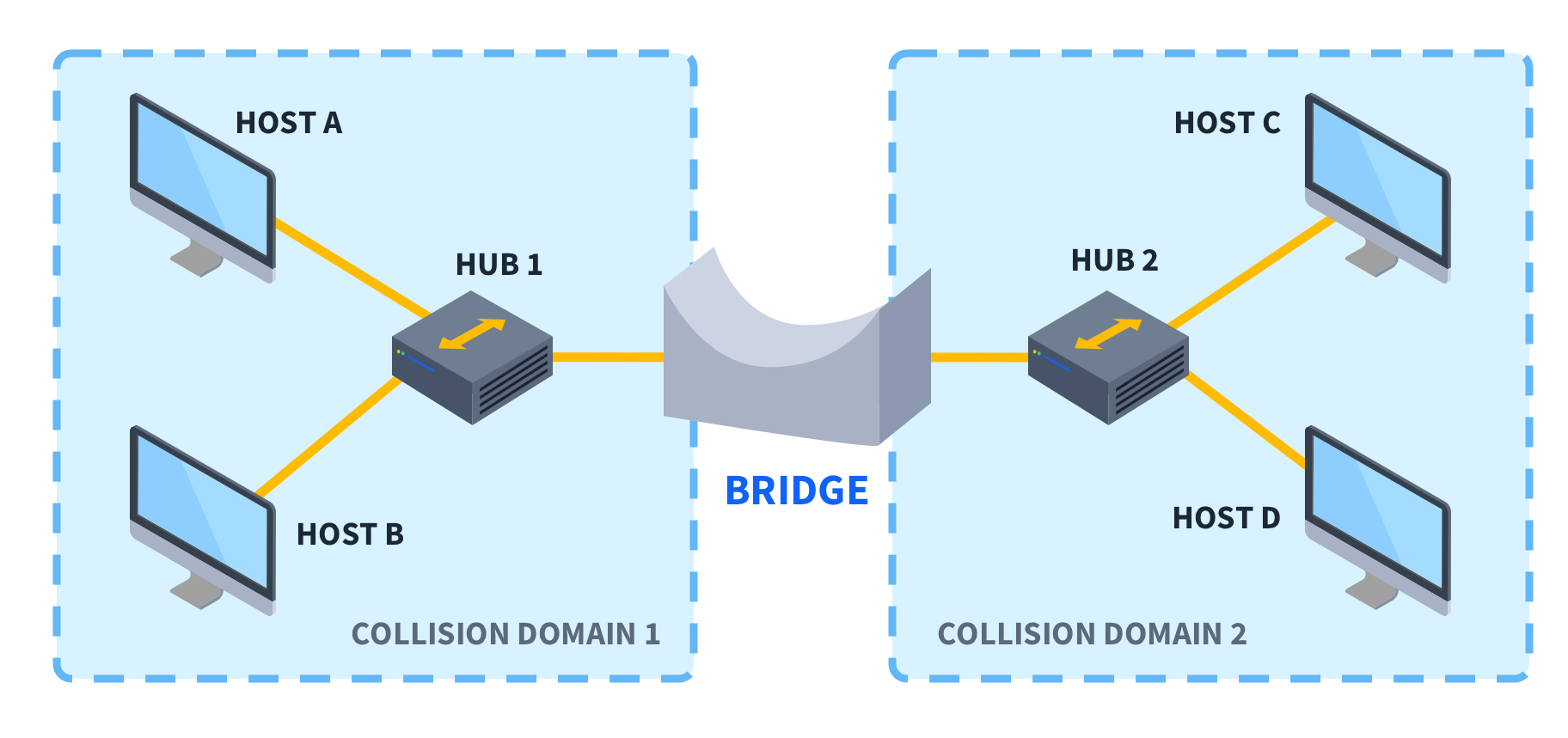
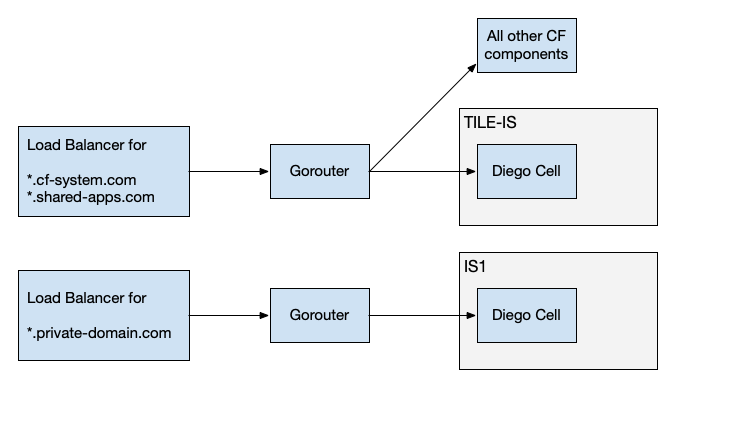
Some key techniques for G Network Configuration for Network Segmentation and Isolation include:- Isolating Backplane Traffic by using VLANs (Logical Segmentation)
- Isolating Backplane Traffic Physically (Physical Segmentation)
- Client Isolation
- Wireless Network Segmentation