Protecting against Zero-Day Malware Attacks
As the name suggests, zero-day malware attacks are a type of cyber threat that takes advantage of unknown software vulnerabilities before developers release security patches. This makes them highly dangerous and difficult to defend against. In this article, we'll explore effective strategies for protecting against zero-day malware attacks and ensuring your organization stays ahead of emerging threats.
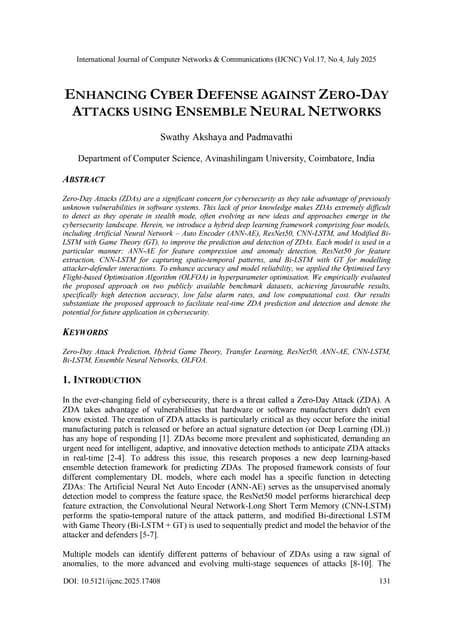
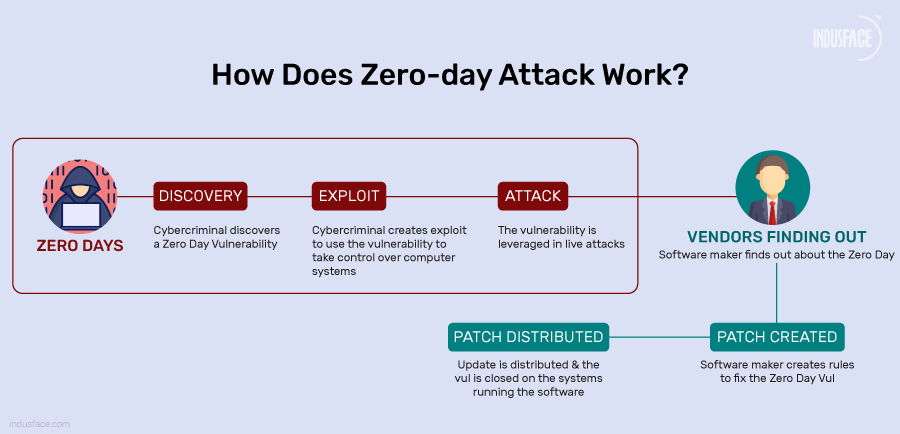
Understanding Zero-Day Malware Attacks
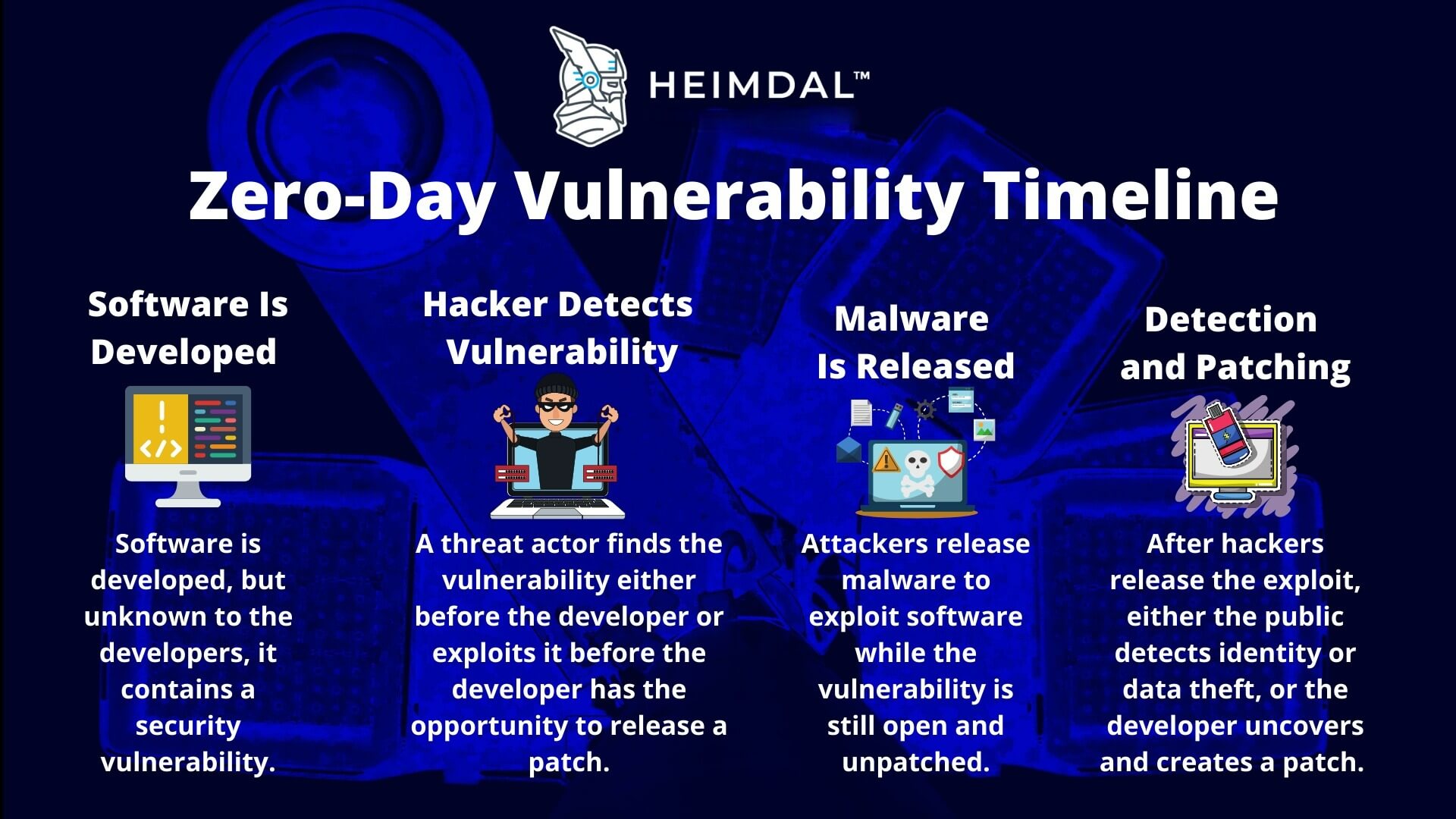
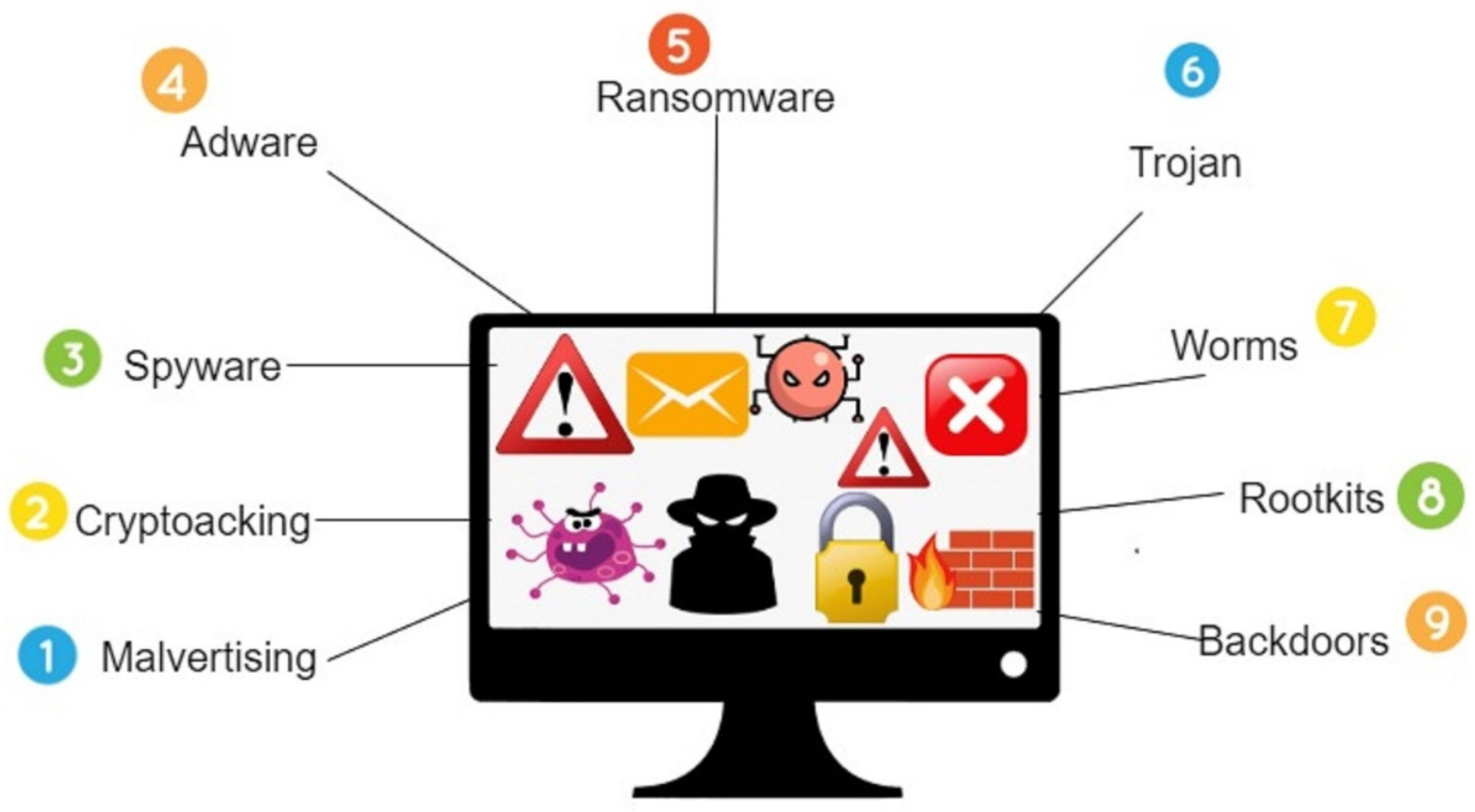
Zero-day malware exploits unknown vulnerabilities before patches exist, giving attackers a window of opportunity to launch a successful attack. These attacks can cause significant damage to your organization's systems, data, and reputation. It's essential to understand the tactics, techniques, and procedures (TTPs) used by attackers to exploit these vulnerabilities and develop targeted defense strategies.
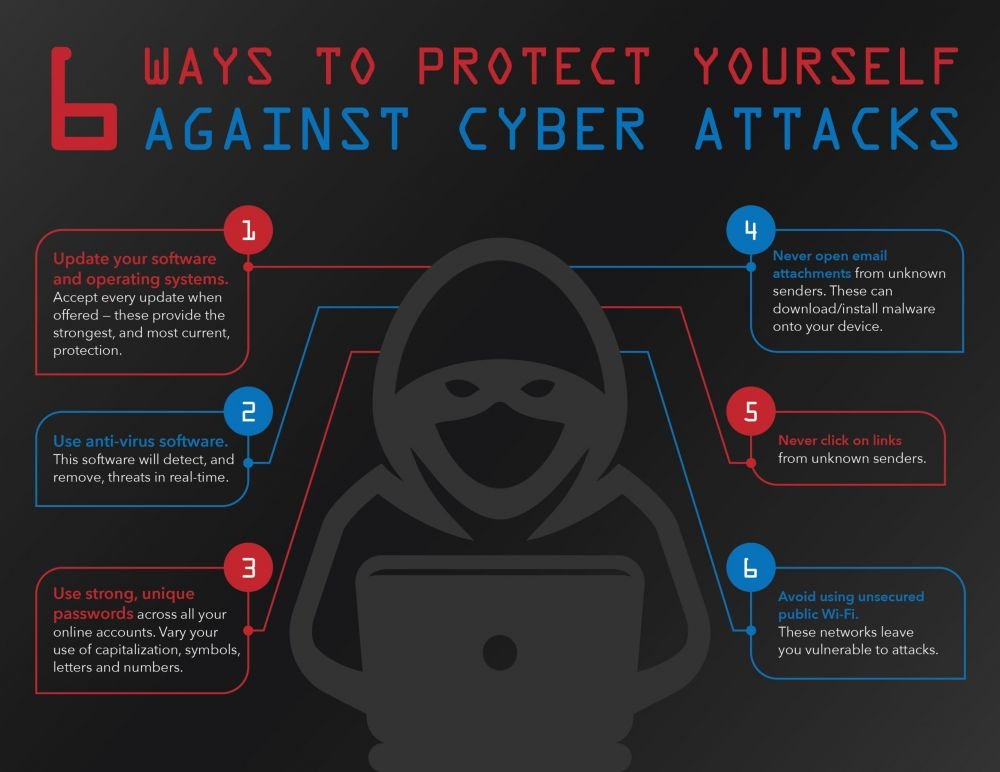
Best Practices to Protect Against Zero-Day Malware Attacks
1. Implement Proactive Detection and Mitigation Strategies
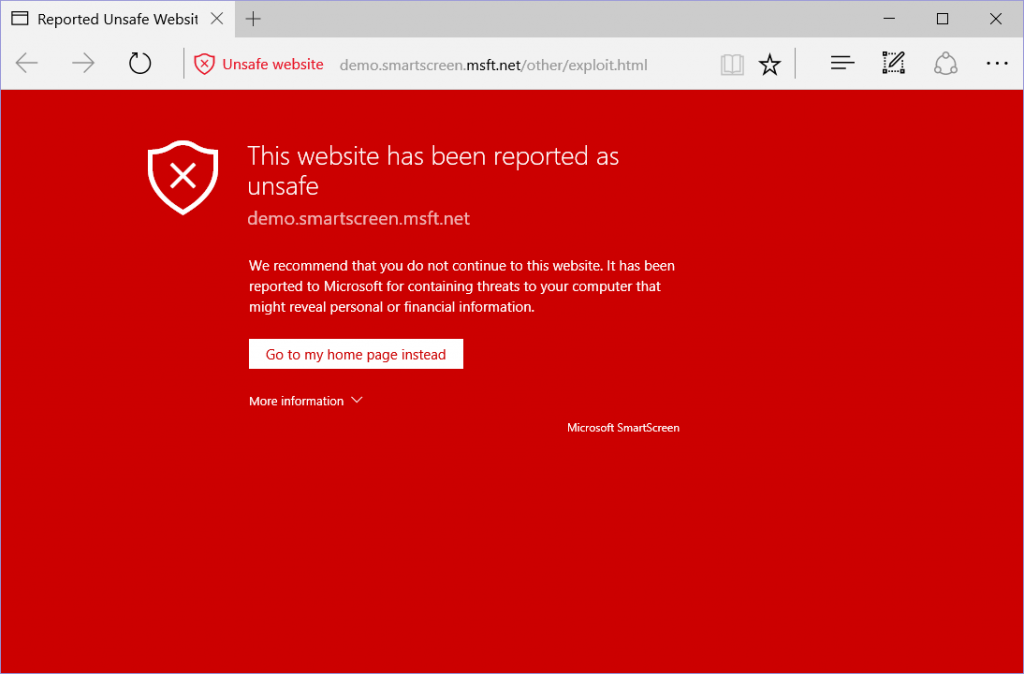
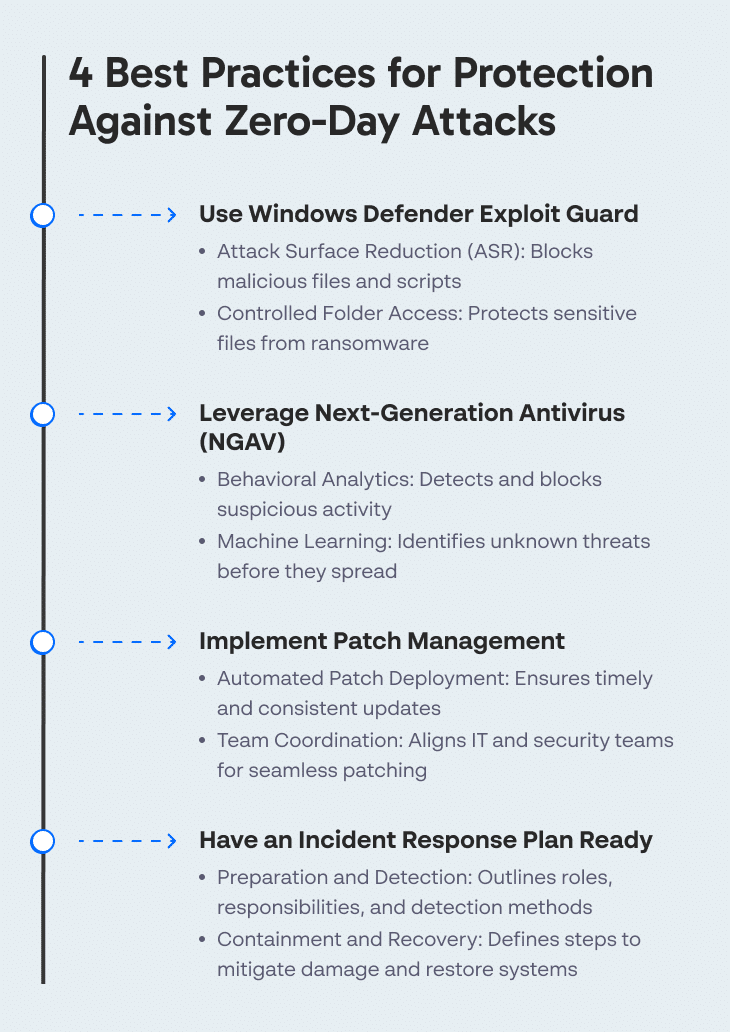
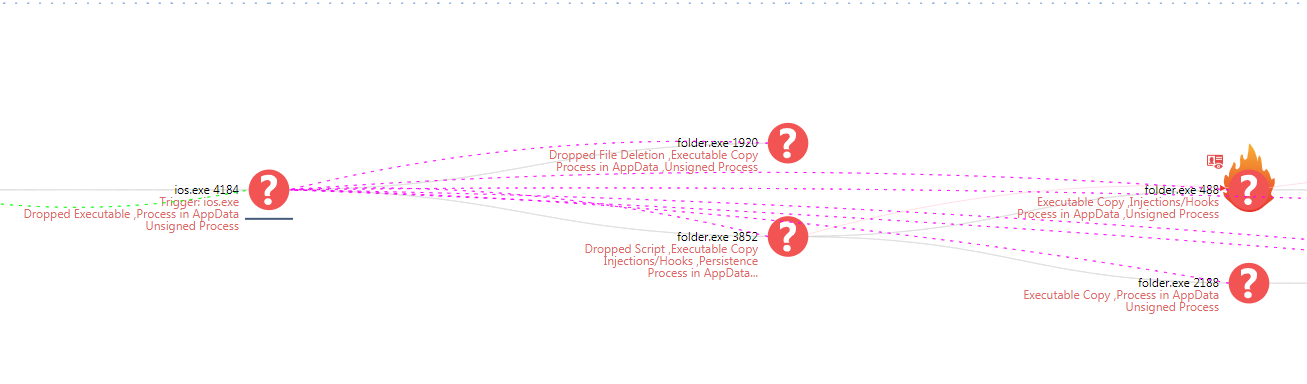
Strengthen zero-day vulnerability protection by implementing proactive detection and mitigation strategies. This includes using advanced threat intelligence, anomaly detection, and machine learning algorithms to identify and mitigate potential threats before they cause harm.

2. Use AI-Powered Security Solutions
AI-powered security solutions can help detect and prevent zero-day malware attacks by spotting patterns and anomalies in system behavior. These solutions can also learn from historical data and adapt to new threats in real-time.
3. Implement Least Privilege Access Controls
Limiting user privileges can help prevent malware from spreading and reduce the attack surface. Implement least privilege access controls to ensure that users only have access to the resources they need to perform their tasks.
4. Regularly Update and Patch Software
5. Educate Users and Implement Phishing Training
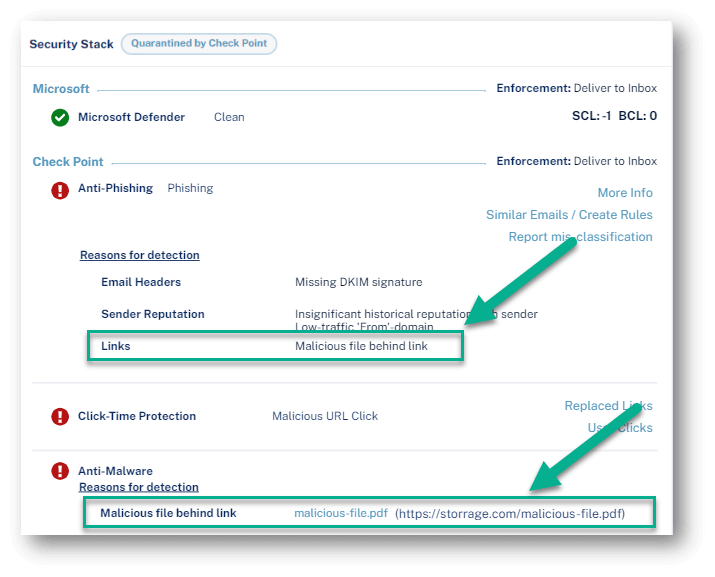
Phishing attacks are a common entry point for zero-day malware attacks. Educate users about phishing tactics and implement phishing training programs to help them identify and report suspicious emails and attachments.
6. Use Multi-Layered Protection
Multi-layered protection involves combining multiple security solutions to provide comprehensive protection against zero-day malware attacks. This can include antivirus software, firewalls, intrusion detection systems, and sandboxing solutions.
7. Monitor and Analyze Network Traffic
Monitoring and analyzing network traffic can help detect and prevent zero-day malware attacks. Use network segmentation and data loss prevention tools to identify and block suspicious traffic.
8. Implement Incident Response Planning

Incident response planning is crucial in the event of a zero-day malware attack. Develop a comprehensive incident response plan that includes procedures for containing, eradicating, and recovering from a malware attack.
Conclusion
Protecting against zero-day malware attacks requires a proactive and multi-faceted approach. By implementing these best practices, you can strengthen your organization's defenses against emerging threats and ensure business continuity. Stay ahead of the game by staying informed about the latest malware threats and best practices for prevention.
Additional Resources
- CISA - Hosts and participates in events throughout the year to engage stakeholders, seek research partners, and communicate with the public to help protect the homeland.
- Sophos Endpoint - Takes a comprehensive, prevention-first approach to security, automatically blocking threats without relying on any single technique.
- Lookout - Delivers end-to-end protection against mobile threats using real-time monitoring and advanced threat intelligence.