Ways to Secure Your Digital Trail
With the increasing reliance on digital technology, our online activities leave behind a trail of data that can reveal a lot about us. This "digital footprint" can be used by organizations to learn more about us, and in some cases, it can even make our personal information vulnerable to compromise. To safeguard our online identity and prevent identity theft, it's essential to understand the concept of a digital footprint and learn ways to secure it.
What is a Digital Footprint?

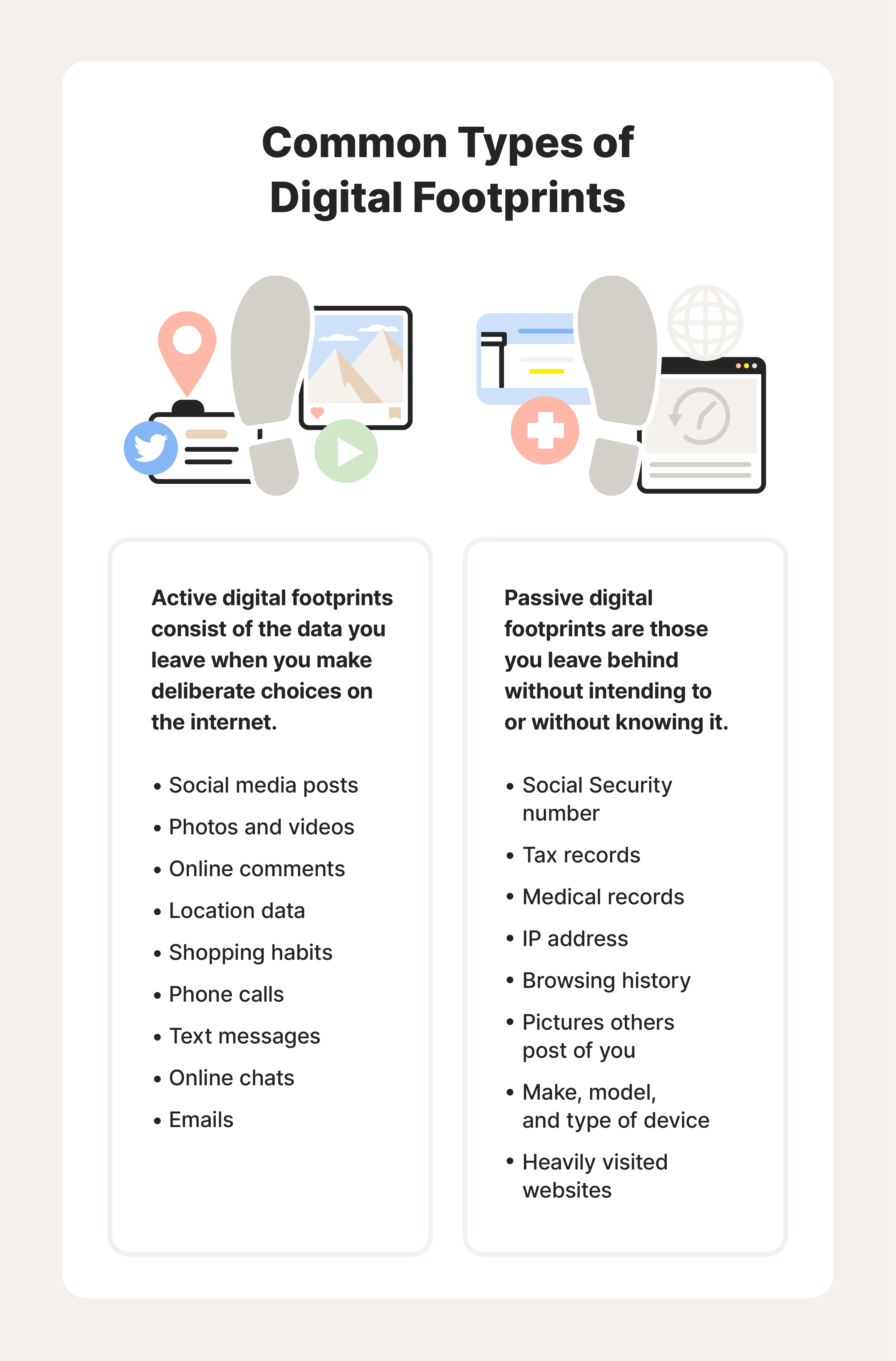
A digital footprint refers to the trail of data we leave behind as we navigate the internet. This includes websites visited, emails sent, social media activity, and search queries. Our digital footprint can be active (data we intentionally share online) or passive (data collected by third parties without our knowledge). The more information we share online, the larger our digital footprint becomes, and the more vulnerable we are to identity theft and data breaches.
Types of Digital Footprints

This particular example perfectly highlights why Ways To Secure Your Digital Trail is so captivating.
There are several types of digital footprints, including:
- Active Digital Footprint: This refers to the data we intentionally share online, such as our social media profiles, blog posts, and online purchases.
- Passive Digital Footprint: This refers to the data collected by third parties without our knowledge, such as our browsing history, search queries, and location data.
- Passive/Active Digital Footprint: This refers to the data we intentionally share online that can be used to infer more information about us, such as our social media profiles that contain our location data.

This particular example perfectly highlights why Ways To Secure Your Digital Trail is so captivating.
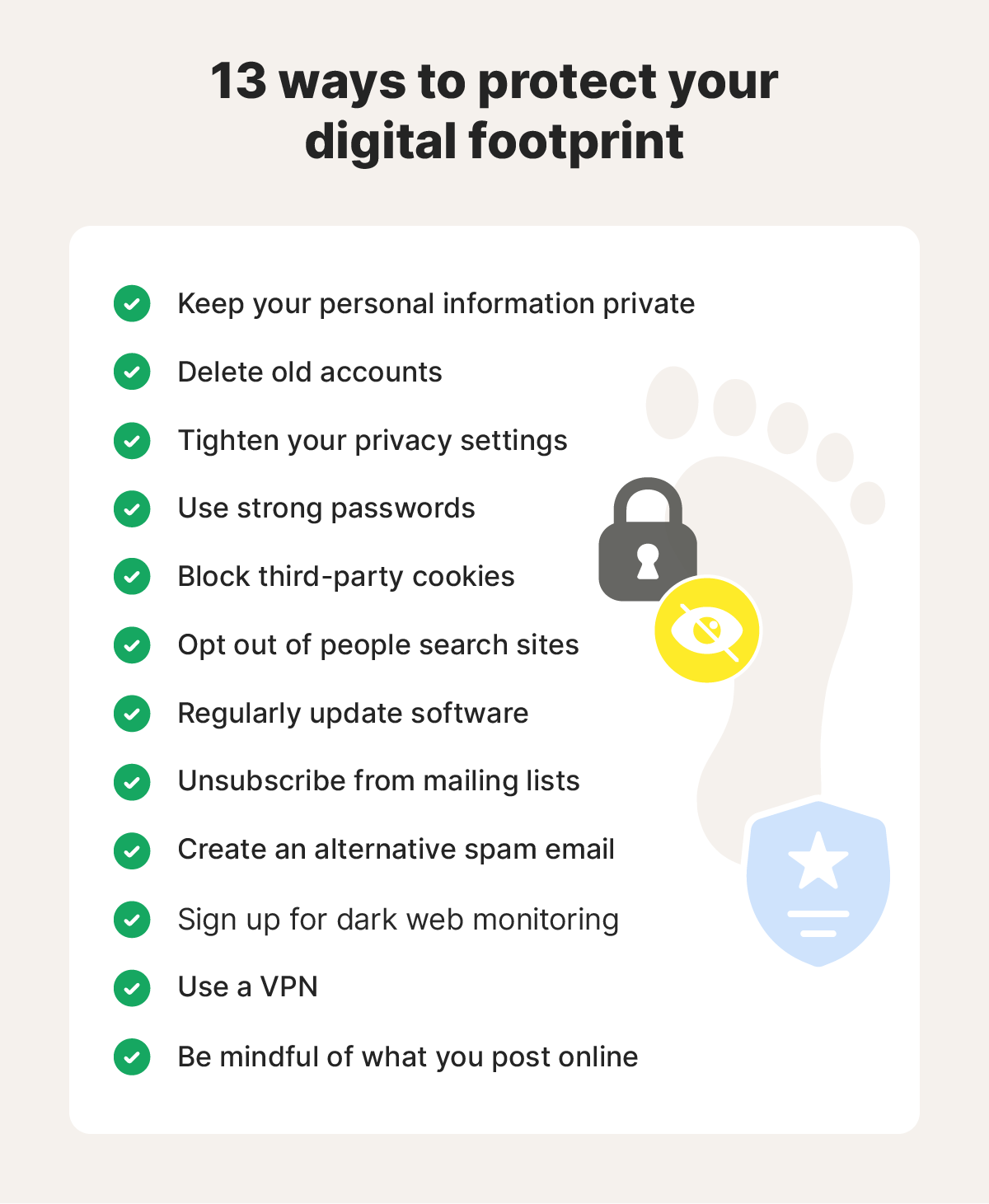
To minimize the risks associated with our digital footprint, here are some ways to secure it:
- Use a Virtual Private Network (VPN): A VPN creates a secure and encrypted connection between your device and the internet, masking your IP address and location data.
- Use a Secure Web Browser: A secure web browser, such as Tor, can help you browse the internet anonymously and securely.
- Use Two-Factor Authentication (2FA): 2FA adds an extra layer of security to your online accounts by requiring a second form of verification, such as a code sent to your phone or a biometric scan.
- Use a Password Manager: A password manager can help you generate and store unique, complex passwords for each of your online accounts.
- Be Cautious with Social Media: Be mindful of the information you share on social media and adjust your privacy settings to limit who can see your posts.
- Use Encryption: Encrypt your data to prevent unauthorized access, especially when sharing sensitive information online.
- Regularly Update Your Software: Regularly update your operating system, browser, and other software to ensure you have the latest security patches.
- Monitor Your Online Activity: Regularly monitor your online activity to detect any suspicious activity or unauthorized access to your accounts.
- Use a Digital Footprint Tracker: A digital footprint tracker can help you identify and manage your online activity, making it easier to secure your digital trail.
Conclusion
Securing your digital trail requires a combination of technical and non-technical measures. By understanding the concept of a digital footprint and taking steps to secure it, you can minimize the risks associated with online identity theft and data breaches. Remember, a secure digital trail is not just about protecting your personal information; it's also about maintaining your online reputation and ensuring your digital security.