G Network Setup for Threat Intelligence
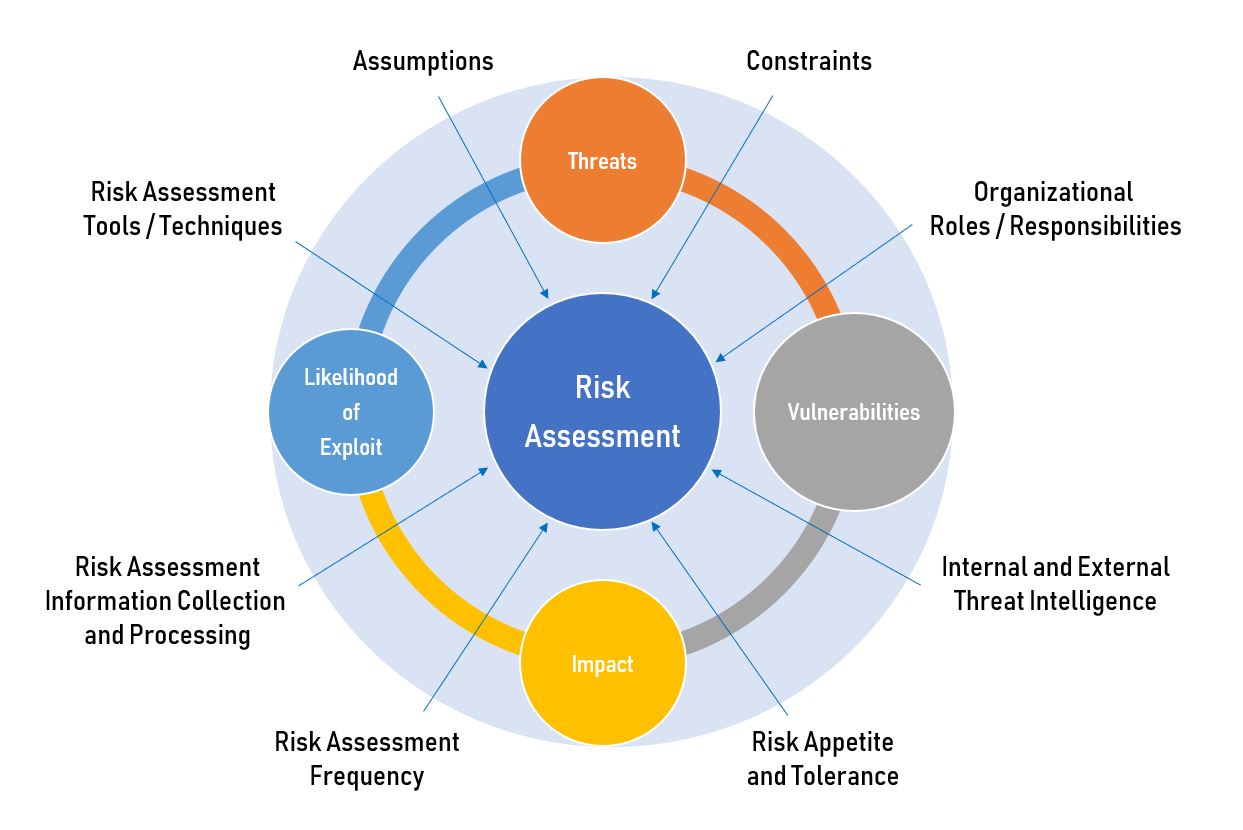
Threat intelligence is a crucial aspect of modern cybersecurity, enabling organizations to stay ahead of potential threats and protect themselves against cyber attacks. A well-designed G Network setup for threat intelligence is the first step towards effective threat detection and mitigation. In this article, we will explore the key components and considerations for setting up a robust G Network framework for threat intelligence.
Introduction to Threat Intelligence
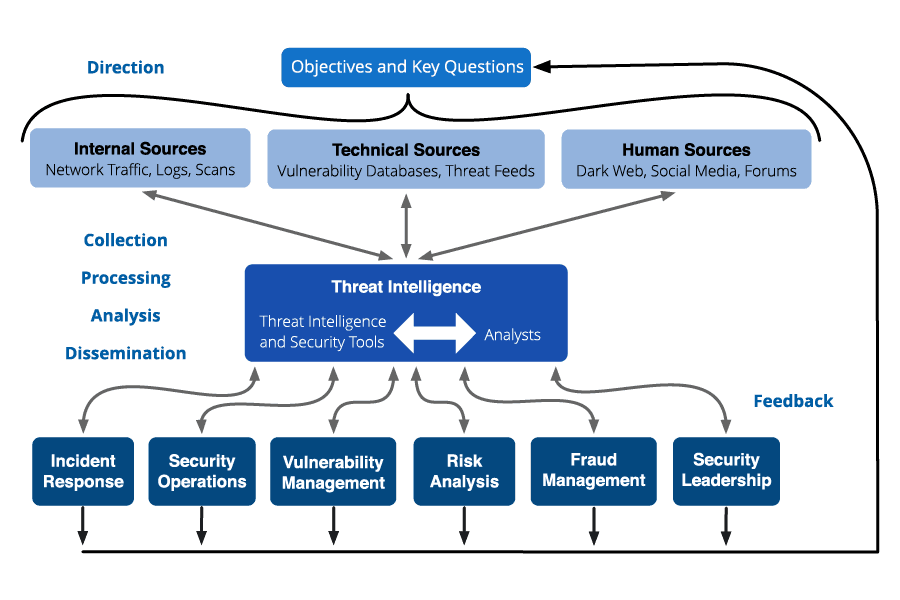
Threat intelligence refers to the collection, processing, and analysis of data to understand an attacker's motives, targets, and attack methods. It transforms raw data into actionable insights, enabling security teams to make informed, data-driven decisions. Threat intelligence is critical for organizations to stay ahead of potential threats and protect themselves against cyber attacks.

A comprehensive G Network setup for threat intelligence involves several key components:
Configuration and Setup
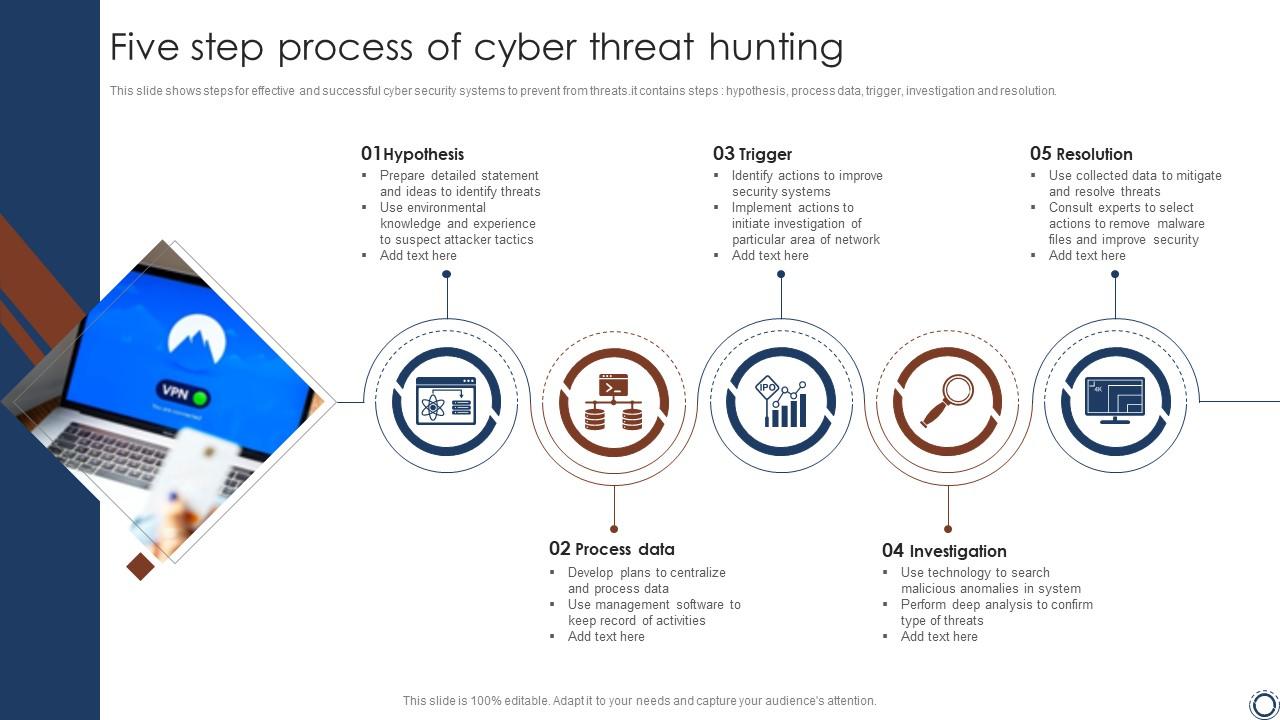
Configuring and setting up a G Network framework for threat intelligence requires careful planning and execution. Here are the steps to follow:

-
Register for a VirusTotal Account
-
Configure the MCP Server
Configure the MCP server using environment variables, adding the VirusTotal API key to enable interactions with the Google Threat Intelligence API.
-
Setting Up Threat Intelligence Feeds
Setup threat intelligence feeds by collecting data from various sources, including network telemetry, SIEM systems, and human intelligence teams.
-
Configure SIEM Systems
Configure SIEM systems to collect and analyze security-related data from various sources, including log files, network traffic, and threat intelligence feeds.
-
Implement Threat Intelligence Framework
Implement a threat intelligence framework to collect, process, and analyze threat data, detect threats, and alert security teams.
Benefits of a G Network Setup for Threat Intelligence
A well-designed G Network setup for threat intelligence provides several benefits, including:

Such details provide a deeper understanding and appreciation for G Network Setup For Threat Intelligence.
-
Improved Threat Detection
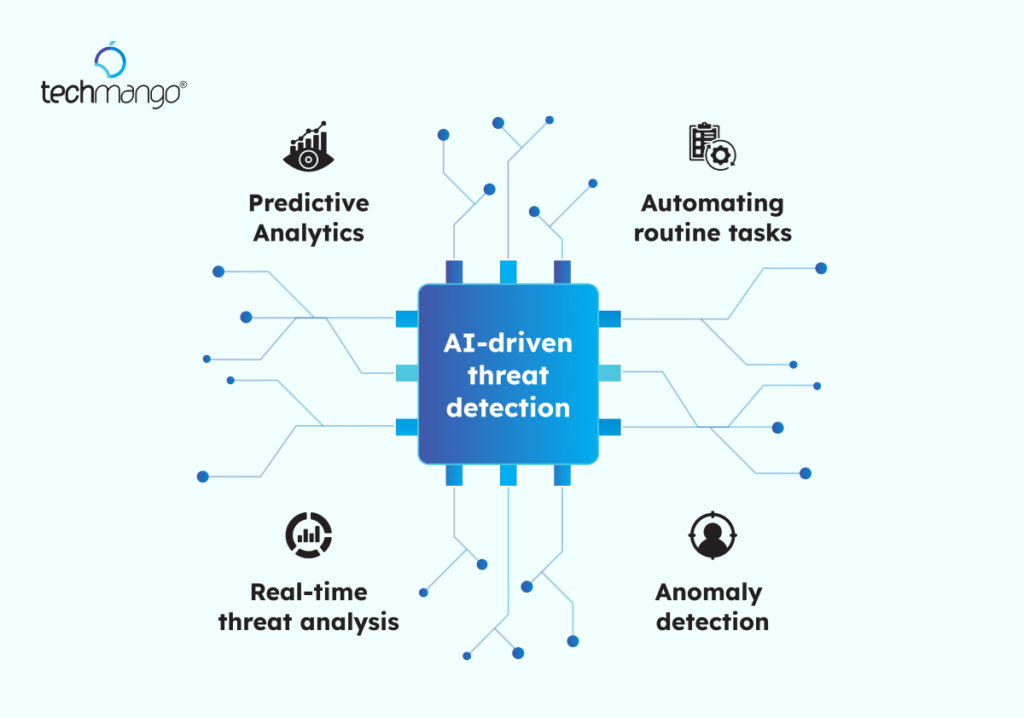
A G Network setup for threat intelligence enables organizations to detect potential threats more effectively, reducing the risk of security breaches and cyber attacks.
-
Enhanced Incident Response
With a G Network setup for threat intelligence, organizations can respond quickly and effectively to security incidents, minimizing the impact of attacks and reducing downtime.
-
Increased Efficiency
A G Network setup for threat intelligence automates many threat detection and response processes, freeing up security teams to focus on higher-level tasks and more strategic initiatives.
Conclusion
Setting up a G Network framework for threat intelligence is a critical step towards effective threat detection and mitigation. By implementing a threat intelligence framework, collecting and analyzing network telemetry, configuring SIEM systems, and setting up threat intelligence feeds, organizations can improve threat detection, enhance incident response, and increase efficiency. A well-designed G Network setup for threat intelligence enables organizations to stay ahead of potential threats and protect themselves against cyber attacks.
















![What is Cyber Threat Intelligence? [Beginner's Guide] | CrowdStrike What is Cyber Threat Intelligence? [Beginner's Guide] | CrowdStrike - G Network Setup For Threat Intelligence](https://media.executivegov.com/2023/07/18/89/57/89/b0/06/f9/8e/d4/5G_1200x628.jpg)