G Router Configuration with Router Security: A Step-by-Step Guide
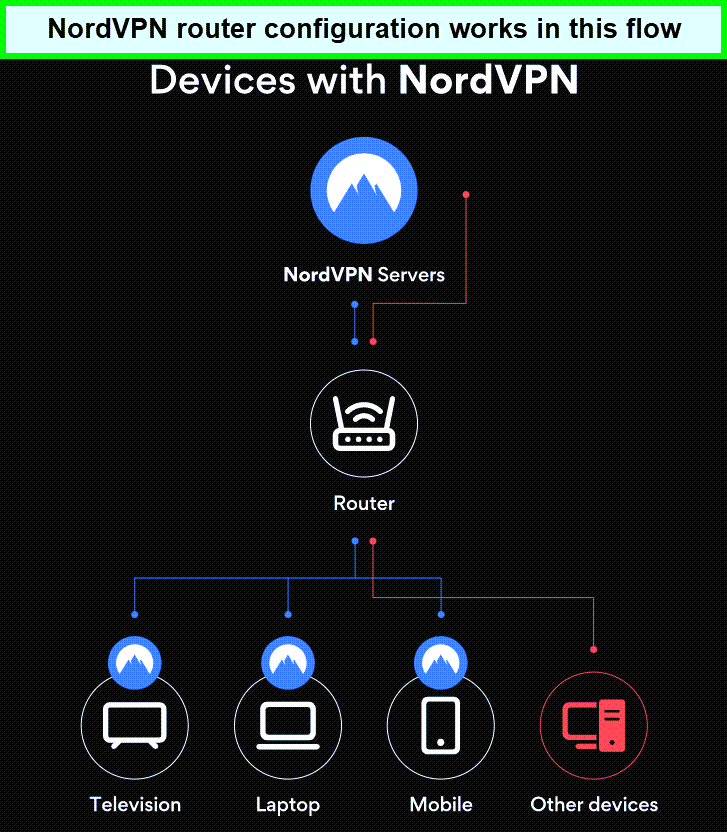
Configuring your G router with top-notch security measures is essential to safeguard your network and connected devices from potential cyber threats. In this comprehensive tutorial, we'll walk you through the step-by-step process of configuring your G router to maintain a secure connection and prevent potential cyberattacks.
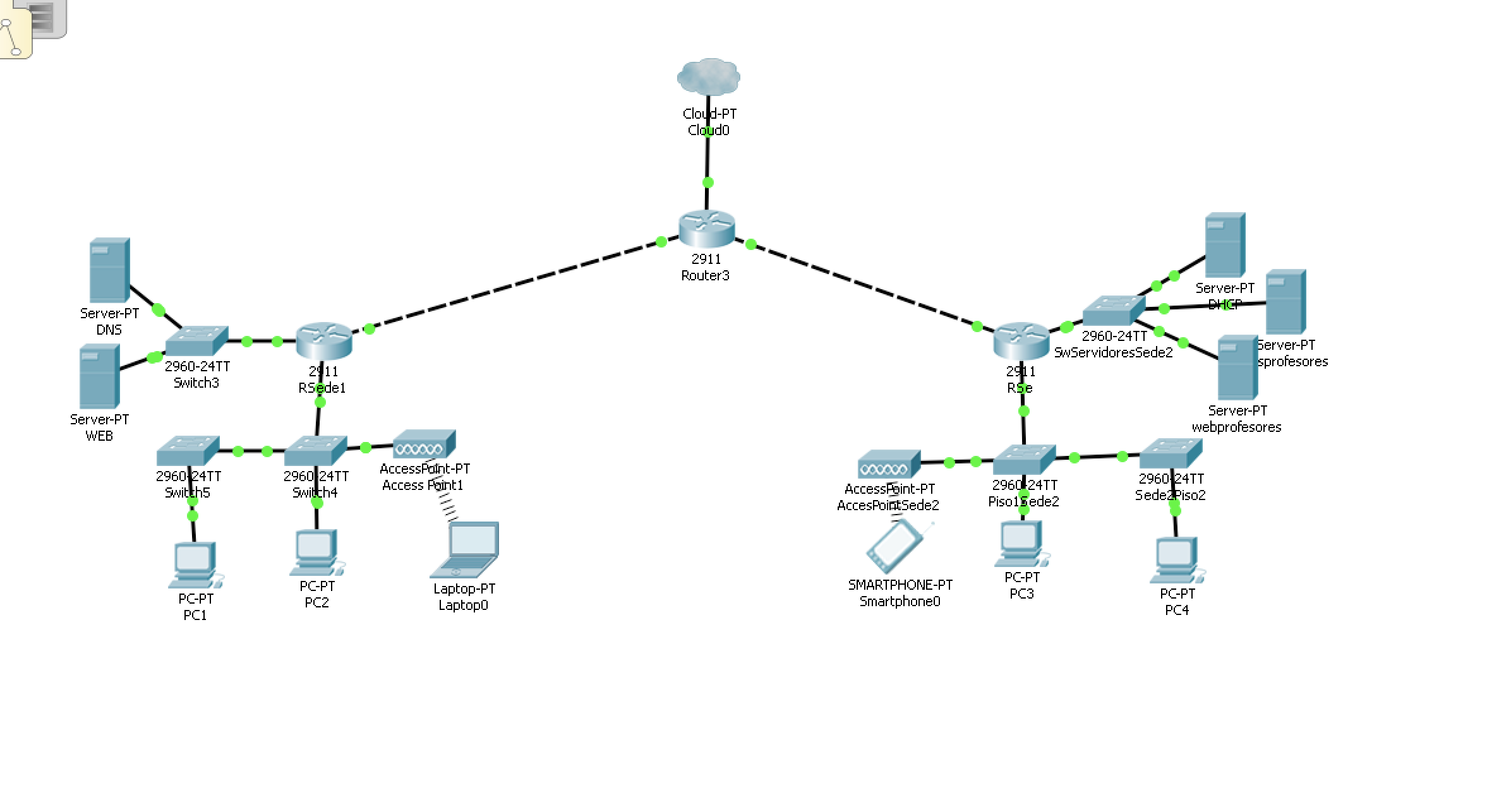
Why G Router Configuration with Router Security Matters
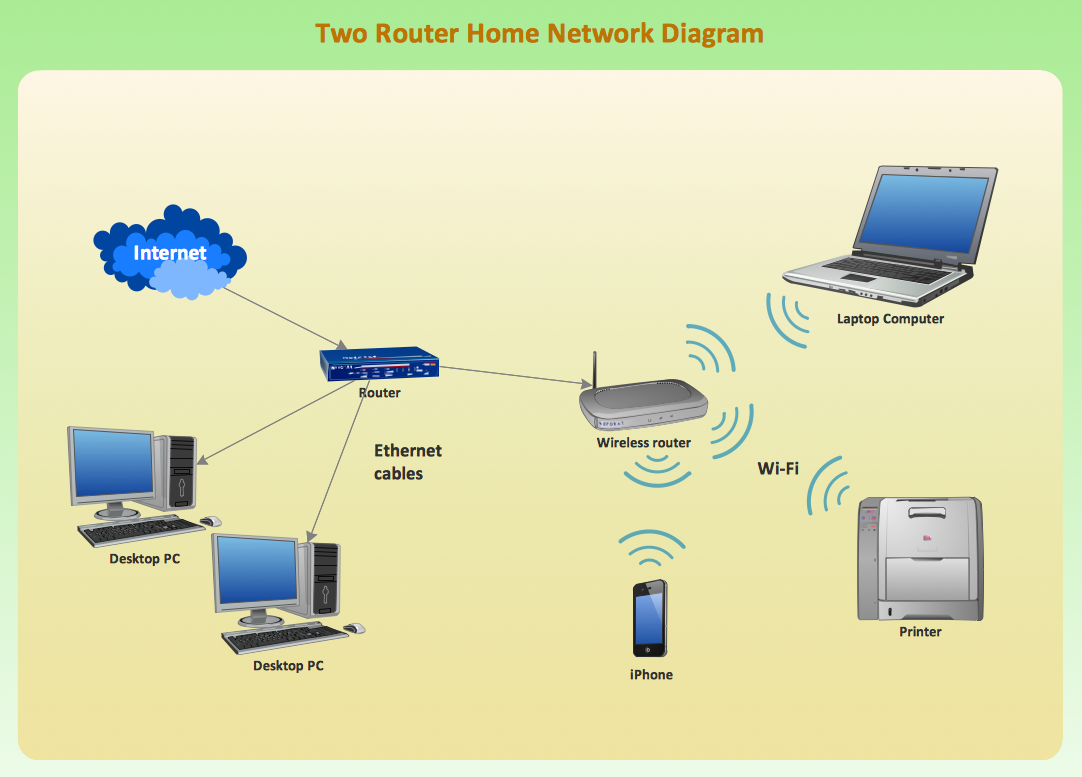
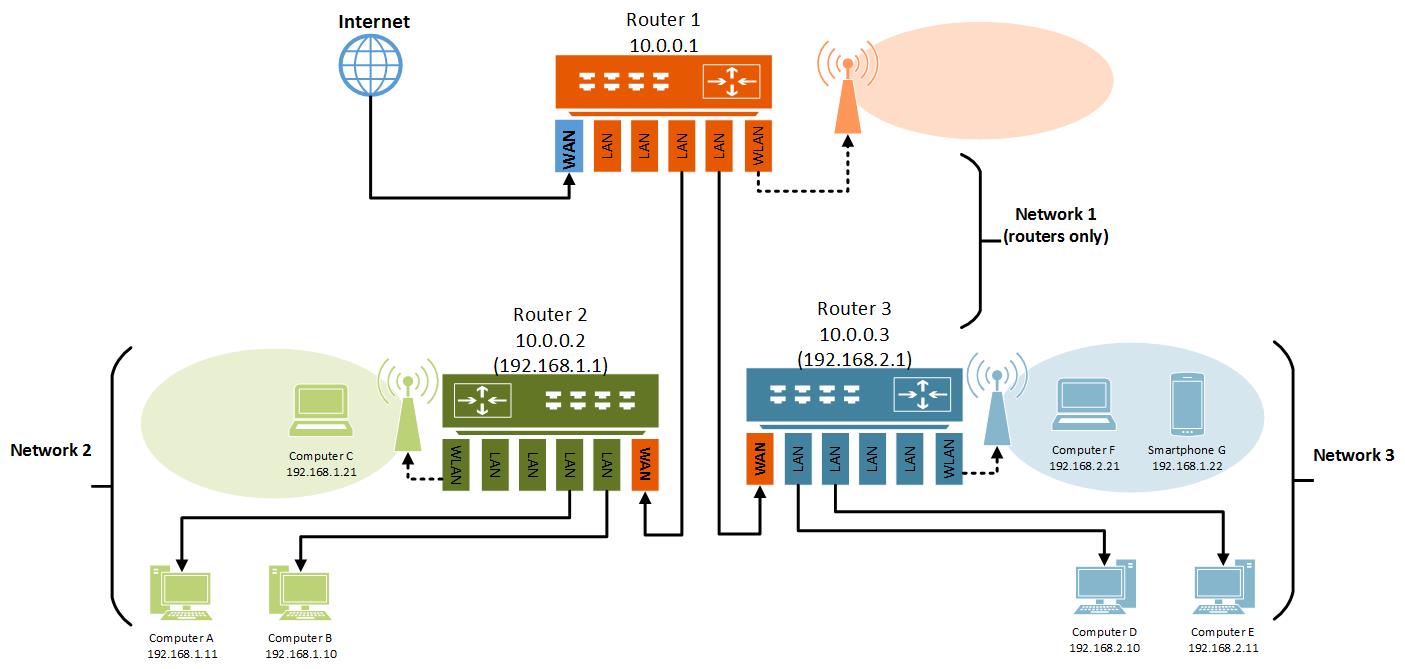
A G router is a powerful device that connects your devices to the internet, but it's also a potential entry point for hackers and cyber threats. By configuring your G router with robust security features, you can ensure the privacy and protection of your network and connected devices. A properly configured G router will also help prevent data breaches, ransomware attacks, and other cyber threats.
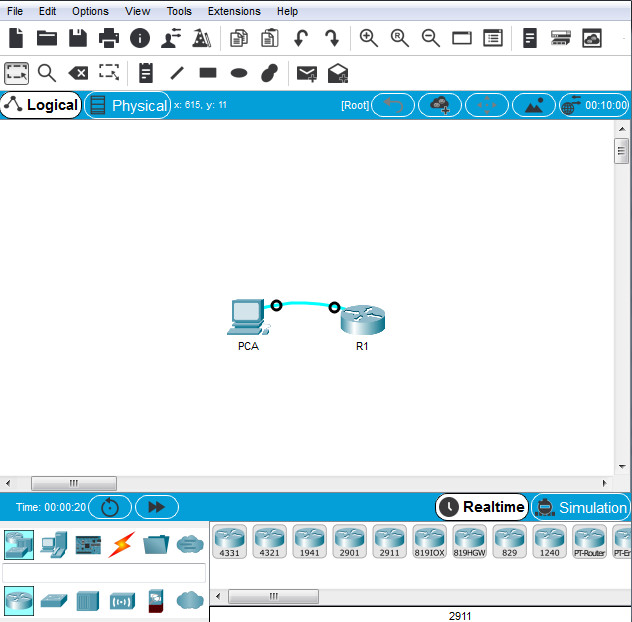
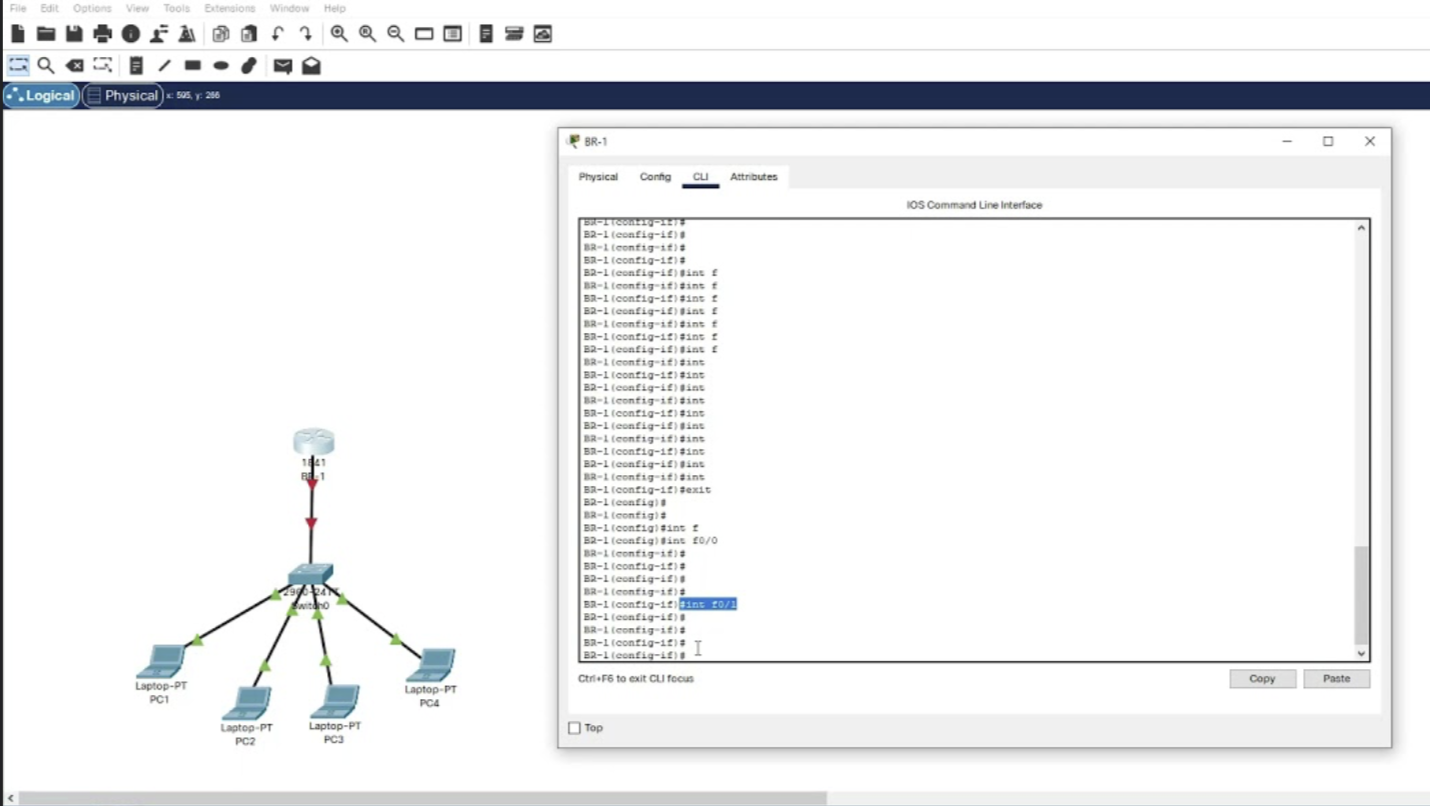
Step 1: Access Your G Router's Web Interface
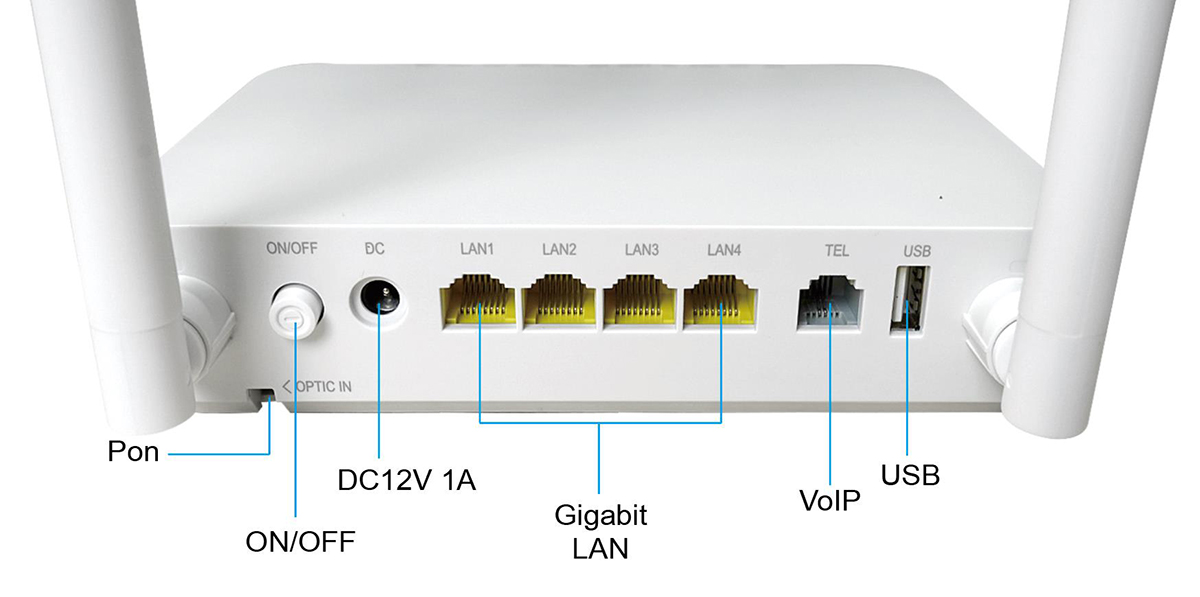
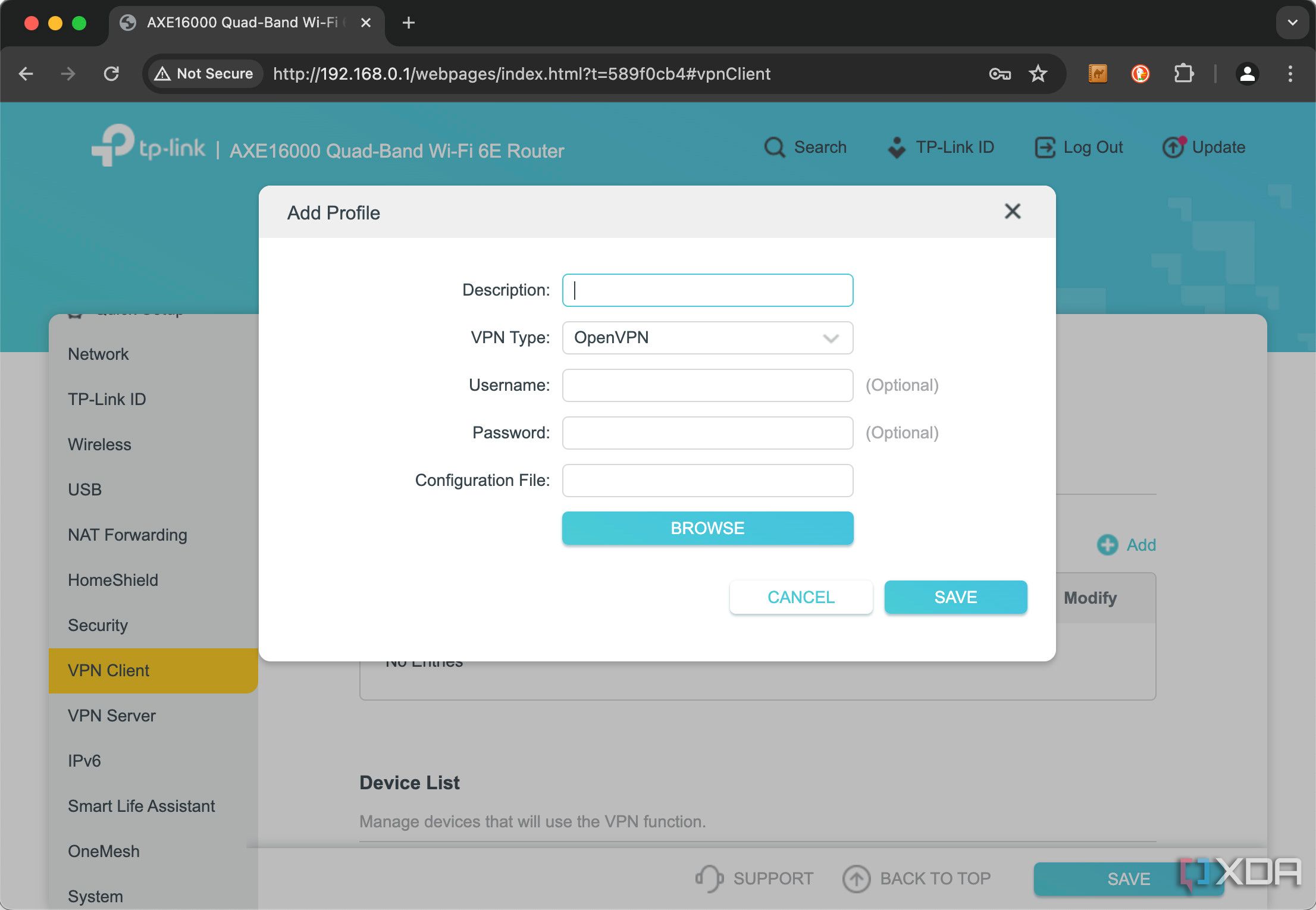
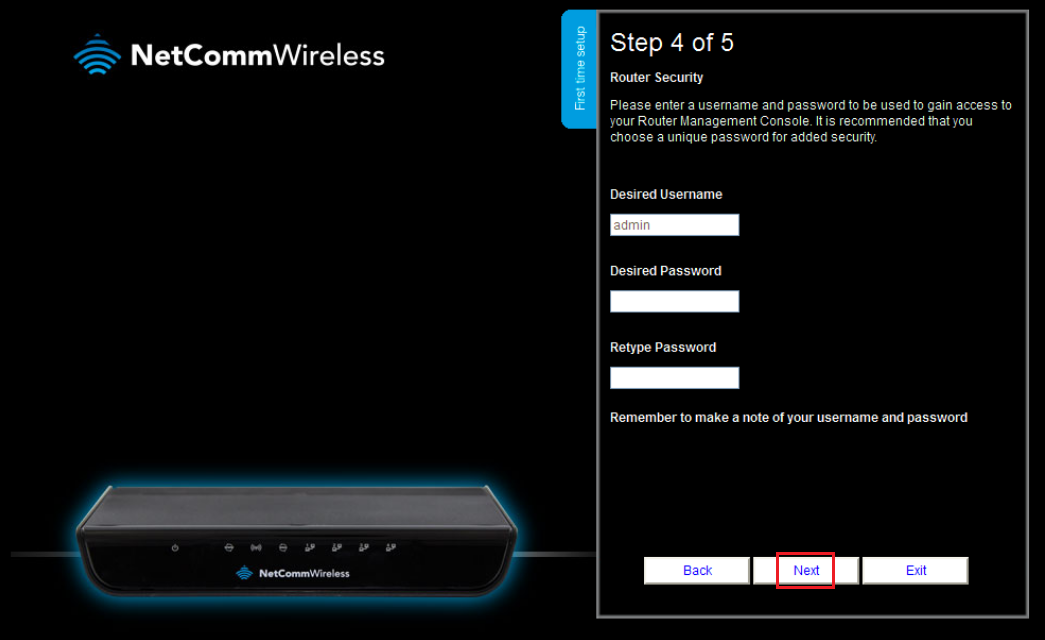
To access your G router's web interface, open a web browser and type the router's IP address in the address bar. The default IP address for most G routers is 192.168.0.1 or 192.168.1.1. Log in to your router using the administrator username and password, which can usually be found on the underside of the router or in the user manual.
As we can see from the illustration, G Router Configuration With Router Security has many fascinating aspects to explore.
Step 2: Change Your Administrator Password
Change your administrator password to a strong and unique password to prevent unauthorized access to your router's web interface. Make sure the password is a combination of uppercase and lowercase letters, numbers, and special characters.
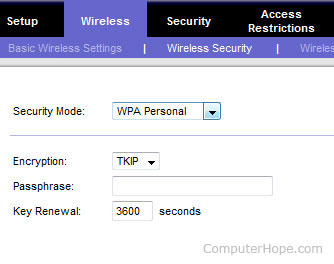
Step 3: Enable WPA2 Encryption
Enable WPA2 encryption to secure your wireless network and protect it from hackers and cyber threats. WPA2 is the most secure encryption protocol available for wireless networks.
Step 4: Set Up Firewall Rules

Such details provide a deeper understanding and appreciation for G Router Configuration With Router Security.
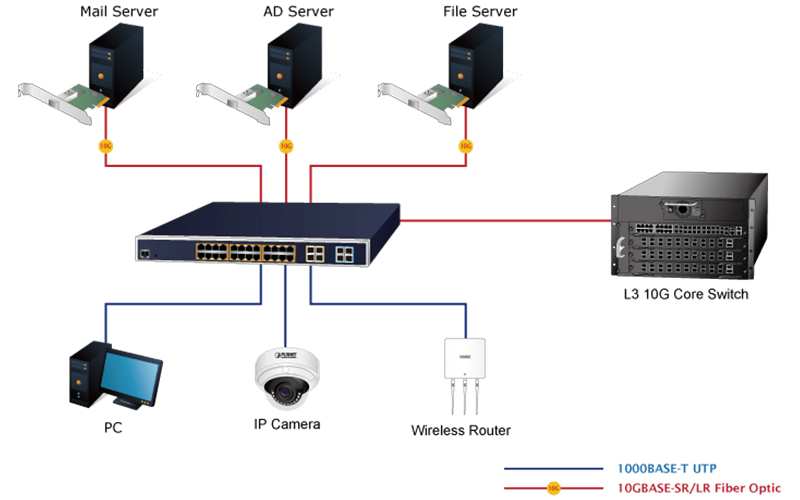
Set up firewall rules to block incoming and outgoing traffic on your network. This will help prevent unauthorized access to your network and protect it from malware and other cyber threats.
Configure DMZ (Demilitarized Zone) settings to isolate your public services, such as FTP, SSH, and Web servers, from your private network.
Step 6: Update Your Router's Firmware
Update your router's firmware to ensure you have the latest security patches and features. Firmware updates can help prevent known vulnerabilities and improve your router's overall performance.
Step 7: Set Up Parental Controls

Set up parental controls to restrict access to certain websites, set time limits, and monitor online activity. This will help keep your children safe online and prevent cyber threats.
Conclusion
Configuring your G router with robust security features is crucial to safeguard your network and connected devices from potential cyber threats. By following these step-by-step instructions, you can ensure the privacy and protection of your network and connected devices. Remember to always keep your router's firmware up to date and update your passwords regularly to maintain optimal security.
Frequently Asked Questions
- Q: What is the default IP address for most G routers? A: The default IP address for most G routers is 192.168.0.1 or 192.168.1.1.
- Q: How do I access my G router's web interface? A: To access your G router's web interface, open a web browser and type the router's IP address in the address bar.
- Q: What is WPA2 encryption? A: WPA2 is the most secure encryption protocol available for wireless networks.
- Q: What is a DMZ (Demilitarized Zone)? A: A DMZ is a network segment that separates a public service from a private network.
- Q: How do I update my router's firmware? A: To update your router's firmware, go to your router's web interface and follow the instructions to update the firmware.

![[AI Router] AiProtection Smart Security Introduction and Setup Image showcasing [AI Router] AiProtection Smart Security Introduction and Setup](https://sp-uploads.s3.amazonaws.com/uploads/services/5157812/20221010192153_634470d144f2c_5_routers_configuration_coding__cisco_packet_tracer_page0.jpg)


![[Wireless Router] How do I enter my ASUS router's setting page using ... Picture of [Wireless Router] How do I enter my ASUS router's setting page using ...](https://img.freepik.com/premium-vector/isometric-flat-3d-illustration-concept-wifi-router-security-analyzer_18660-4913.jpg)